-
Rely on guaranteed
IT services
-
Sleep better at night
-
Look forward
to Monday morning
Turn Technology Troubles Into Triumphs
-
Do you fight the same tech fires over and over again?
-
Are you working without a technology strategy and hoping you can just wing IT?
-
Do small inefficiencies add up to a big drag on your company?
-
Are you dealing with a mess of aging computers, cobbled together networks and frustrated employees?
-
Are you worried about cybersecurity and compliance?
If these frustrations sound familiar, we understand.
Our team of experienced network administrators and systems engineers have been helping businesses streamline their IT solutions to increase productivity and their bottom line for decades – and we’re ready to help you, too.
IT Support Services That Mean Business
If your business technology feels like a black hole of wasted time and money, it means one thing:
You need better IT support services. After all, technology affects your productivity, profitability and staff morale.
At SynchroNet, we believe technology should help your team work smarter, reduce risk and even become a profit center.
Rely on our team of local caring pros and IT services with predictable, affordable costs.
-
No long-term contracts and true fixed monthly fee
-
Proven process to reduce repeat issues
-
100% “you can’t lose” satisfaction guarantee
-
24/7/365 IT support services In business since 1998
-
80+ clients in a range of complex industries
-
Serving Buffalo and all of Western NY
Sync Up
Your Technology
Move away from disarray:
We’ll provide the tools you need and a process you can trust and no hidden charges or fees.
In fact, SynchroNet pays for itself within 30 to 90 days through improved productivity and immediate reduction of risk, as trouble tickets and issues decrease, and downtime evaporates.
Check our experts for IT consulting and get the best deal right now.
IT Support Services
Explore our IT support services to learn how we can support your technology needs.
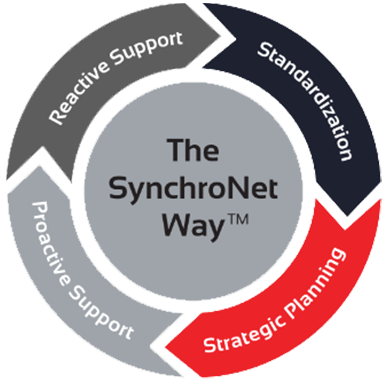
The SynchroNet Way
Want to move your business IT from the wild, wild West to an island of serenity? We get it, and we’ve helped transform everyday work life for hundreds of clients using The SynchroNet Way.
With our approach you get:
-
Standardization and a 100-point Best Practices checklist assigned to a dedicated network administrator.
-
Strategic planning at an executive level with a dedicated vCIO that keeps you on track for the long run.
-
Proactive support that monitors and protects your systems around the clock.
-
Reactive support from our friendly and caring customer support team who are always on the lookout for repeat issues.
SynchroNet Customers Say

IT Consulting Buffalo: Real-World Solutions
-
Legacy System Overhaul: Many businesses in Buffalo still operate with outdated systems that slow down workflows. IT consulting focuses on identifying critical pain points, upgrading legacy systems, and ensuring compatibility with modern tools—all while minimizing downtime.
-
Custom Automation Strategies: Instead of relying on off-the-shelf solutions, IT consulting helps design automation tailored to your processes, reducing repetitive tasks and freeing up resources for high-priority work.
-
Disaster Recovery Planning: Whether it’s natural disasters or cyber threats, IT consulting ensures you have a clear disaster recovery plan with data backups, system redundancies, and fast recovery times to keep operations running.
-
Hybrid Infrastructure Setup: With the rise of remote work, IT consulting provides expertise in creating secure, hybrid IT infrastructures, combining on-site systems with cloud solutions for maximum flexibility and cost-effectiveness.
SynchroNet delivers focused, problem-solving IT consulting that addresses real-world challenges, making it highly relevant and valuable to your business needs.
IT Support Insights & Outlook

The “Summer Friday” Security Checklist: Protecting Buffalo and WNY Businesses on the Go
Because Your Business Needs Better IT Support

If you’re having the same IT issues over and over again, you’re wasting time and not getting the most from the people you’ve hired.
Not having the IT support services you need could be hurting your productivity and bottom line.
Let us show you a more predictable and efficient approach to technology.
Before You Go
Grab a Snack
Cybersecurity Essentials Checklist
Download SynchroNet’s Cybersecurity Essentials Checklist to make sure your business is protected against all unprecedented threats.
The list is created by our cybersecurity experts and it maps out 13 key areas of focus to help you keep your data and people safe, secure and productive.
Three Steps To Better IT

Tell us about your business

Get a plan to grow with the right technology